Phishing
Check out Wizer's 1:21 minute video about how scammers will prey on your emotions to get a reaction out of you.
For examples of phishing emails received on campus and more information, visit our Phishing Emails webpage.
Always report any suspicious emails in your UTHSC account to abuse@uthsc.edu or call Service Desk at 901.448.2222 ext. 1 immediately.
Phishing
Phishing attacks use email or malicious websites (clicking on a link) to collect personal and financial information or infect your machine with malware and viruses.
Spear Phishing
Spear phishing is highly specialized attacks against a specific target or small group of targets to collect information or gain access to systems.
For example, a cybercriminal may launch a spear phishing attack against a business to gain credentials to access a list of customers. From that attack, they may launch a phishing attack against the customers of the business. Since they have gained access to the network, the email they send may look even more authentic and because the recipient is already customer of the business, the email may more easily make it through filters and the recipient maybe more likely to open the email.
The cybercriminal can use even more devious social engineering efforts such as indicating there is an important technical update or new lower pricing to lure people.
Spam
Spam is the electronic equivalent of junk mail. The term refers to unsolicited, bulk – and often unwanted – email. Here are ways to reduce spam:
- Enable filters on your email programs: Most ISPs (Internet Service Providers) and email providers offer spam filters. However, depending on the level you set, you may wind up blocking emails you want. It's a good idea to occasionally check your junk folder to ensure the filters are working properly.
- Report spam: Most email clients offer ways to mark an email as spam or report instances of spam. Reporting spam to abuse@uthsc.edu will also help to prevent the messages from being directly delivered to your inbox.
- Own your online presence: Consider hiding your email address from online profiles and social networking sites or only allowing certain people to view your personal information.
Pharming
Pharming leverages malicious code such as viruses, worms, trojans and spyware to carry out sophisticated attacks such as hosts file modification, DNS cache poisoning etc. Pharmers can even hijack domains or spoof static domain names in order to fool users by redirecting them to malicious websites.
The Anatomy of a Pharming Attack
1. The user types in the address of their bank (e.g. www.xyzbank.com) into the address bar of their browser.
2. The request passes to a DNS name server. This server maps www.xyzbank.com to a number such as 210.10.10.3 (IP address, which is understandable to the computers).
3. Normally, the browser connects the user to the authentication site of xyzbank. However, in pharming, the attacker modifies the mapping in the DNS service. Now, DNS service maps www.xyzbank.com to 230.10.10.3 – the IP address of attacker's fake site.
4. The customer thinks that they are interacting with their bank, because it so indicates this http://www.xyzbank.com in the browser's address bar, but they are actually connected to the deceptive site of the attacker.
Social Media
Spam, phishing and other scams aren't limited to just email. They're also prevalent
on social networking sites. The same rules apply on social networks: When in doubt,
throw it out. This rule applies to links in online ads, status updates, tweets and
other posts.
Here are ways to report spam and phishing on social networks:
- Reporting spam and phishing on Facebook
- Reporting spam on Twitter
- Reporting spam and phishing on YouTube

How Do You Avoid Being a Victim?
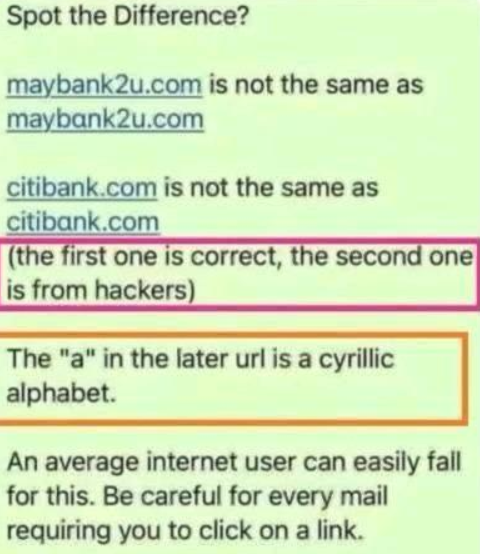
- Don't reveal personal or financial information in an email, and do not respond to email solicitations for this information. This includes following links sent in email. Always hover over hyperlinks to ensure the link is legitimate.
- Do not click an email link and enter or input your UTHSC NetID and/or password.
- Before sending sensitive information over the Internet, check the security of the website.
- Pay attention to the website's URL. Malicious websites may look identical to a legitimate site, but the URL may use a variation in spelling or a different domain (e.g., .com versus .net).
- If you are unsure whether an email request is legitimate, try to verify it by contacting your UTHSC Service Desk or corresponding company directly. Contact the company using information provided on an account statement, not information provided in an email. Information about known phishing attacks is available online from groups such as the Anti-Phishing Working Group.
- Keep a clean machine. Having the latest operating system, software, web browsers, anti-virus protection and apps are the best defenses against viruses, malware, and other online threats.
What to Do if You Think You are a Victim?
- Report it to abuse@uthsc.edu or call Service Desk at 901.448.2222 ext. 1 immediately! We can be alerted for any suspicious or unusual activity.
- If you believe your financial accounts may be compromised, contact your financial institution immediately and close the account(s).
- Watch for any unauthorized charges to your account.
- If you believe your financial and/or business accounts may be compromised, consider reporting the attack to your local police department, and file a report with the Federal Trade Commission or the FBI's Internet Crime Complaint Center.
How to Write a Non-Phishy Email: Do's and Don'ts
Is your department planning to send a survey or ask your students to complete a task online? Do your faculty need to update their information with the department? Sometimes you have to request specific personal information or ask faculty, staff, and students to take action for entirely legitimate reasons. The issue with this kind of email is that it can sound suspiciously similar to the hoax messages sent by phishers.
When sending unsolicited email, it’s important to make the email look trustworthy. Below are some suggestions follow when writing emails to make them look less suspicious.
DO’S AND DON’TS WHEN WRITING EMAIL MESSAGES
From:
- Clearly identify who you are — Your “From” name and email address should accurately identify who is sending the email.
Subject:
- Write a meaningful subject line — Keep it short and be specific about the point of the email. Also, try to arrange the keywords in order of importance to grab people’s attention.
Body
- Provide a detailed explanation — Explain the situation that has caused your department to send this urgent or important
message. Actual phishing emails are generally pretty vague.
Sample Phishing messages: “Important,” or “We need you to verify your account before it is deleted.” - Choose your words carefully — Anything along the lines of “urgent action required” will raise flags.
- Use personalization — Phishers don’t personalize their emails with recipients’ names because they typically don’t have this information. If you do, use it.
- Reference your trusted website — If you need recipients to proceed to a website, send them to your department’s main webpage and prominently display a message with the action that needs to be taken. Do not send them directly to a login page. Phishers will post “fake” login pages to collect credentials.
- Don’t ask people to click a link — To get people to visit your website or log in to their account; it’s best to provide the web address as text only and advise them to type it in. Provide step-by-step instructions when necessary. We realize that links are sometimes unavoidable; if you need to include a link, be sure to link to an information page and not a login screen.
- Don’t forget your address and contact information — Including a physical postal address and accurate contact is not typically something phishers do. Encourage the recipient to contact your office to verify the validity of the message.
Before you send the message
- Check your final draft twice — Spelling errors and poor grammar should be avoided in all campaigns, but it’s especially important in this case because phishing scams commonly contain grammatical errors and misspellings.
Let the UTHSC ITS Service Desk know when you are sending out a mass email that requires a response. This extra step will help us help you. We will be able to quickly answer questions about your email message and encourage the faculty, staff, and students to take action. Please let us know the following information:
- when the email will be sent
- who the target audience is
- who the email is “from”
- contact information if there are questions
- copy of the message
If you would like the Office of Cybersecurity to review your message for phishy-ness, we'll be happy to take a look at it. Contact us at itsecurity@uthsc.edu.