Office of Cybersecurity

Cybersecurity Awareness Month has come and gone! Thanks to everyone who participated, played some games and watched some videos. From phishing tricks to password picks, even small actions can help keep our campuses safe online. Visit our Cybersecurity Awareness page to try out some interactive games we posted throughout October.
Preparedness Topics
In the News
Data for 700M LinkedIn Users Posted for Sale in Cyber-Underground
Colonial Pipeline aims to restore operations by end of the week after cyberattack
Center for Strategic & International Studies Cyber Incidents List
Healthcare Industry Cyberattacks Increase by 45%
Nation State Recruiting via Fraudulent LinkedIn Profiles
Tennessee Couple avoids Publisher's Clearing House Identity Theft Scam
Terminated Worker Accessed PHI After Leaving Job
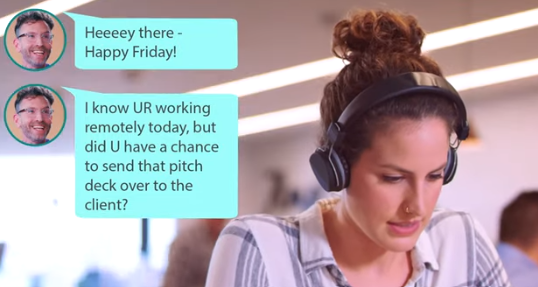
Tesla's employee didn't fall for social engineering and stopped a ransomware attack
Resources
Duo - Don't approve a DUO Push if you haven't initiated it!
The Office of Cybersecurity serves as fundamental technical safeguard for UTHSC. We promote an environment of great ethical standards and observe numerous regulatory risks by:
- Advancing effective ways to prevent security risk through collaboration
- Educating employees and the student body about information security
- Identifying security risks faced by the University.
- Encouraging an ethical environment that encourages information security preventions
- Promoting awareness of information security through outreaching events
- Effective training in the numerous areas of information security
- Providing a workplace that enables employees to participate in the compliance program without fear of retribution.