Phishing Emails

Cybersecurity Alert: Gift Card Scam
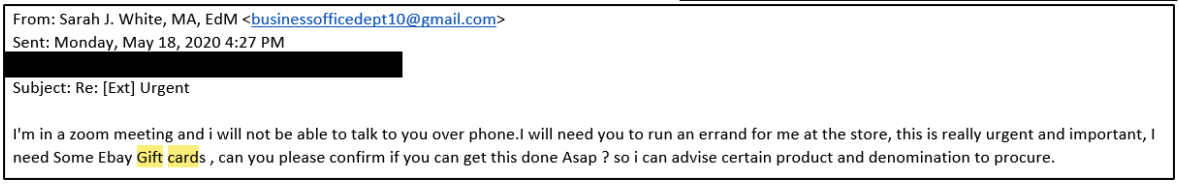
Our campus is being targeted by gift card scam phishing attacks. This type of attack is becoming more common, so we as a campus must remain vigilant to prevent them.
These gift card scam phishing attacks usually begin with an email that will impersonate a dean or manager at UTHSC using a Gmail account. The scammer will create a sense of urgency and ask if you are available and try to get your cell phone number. The scammer will then ask you to purchase gift cards for various retailers and request that you send them the card numbers.
If you receive an email like this, please forward it to abuse@uthsc.edu.
Below are a few examples of what these emails will look like:
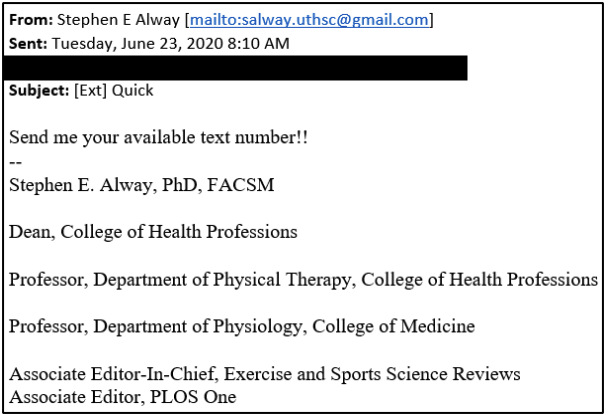
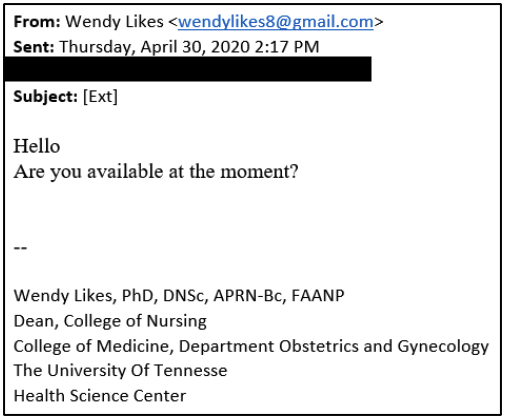
If you receive an email like the one below, or any suspicious email, do not respond, or click on any links, nor open any attachments. Nor provide or enter you NETID and Password in any manner in response to an email. UTHSC will NEVER request your NETID or password. Any major change to systems, software, or applications that may require such actions will be communicated through official UTHSC channels before that change ever occurs.
Report suspicious emails by following the below steps:
In order to report the message effectively, we need the original email sent as an attachment. We have included the instructions below.
- Highlight the spam/phishing message in your inbox.
- For Windows, Press CTRL+ALT+F. For Mac, Control-Command-J. This opens a new email with the highlighted email attached.
- Send it to abuse@uthsc.edu.
- After sending as an attachment, delete the message, delete from your sent folder, and empty your deleted items folder.
Anytime you receive an email you are not sure about, error on the side of caution and follow the above directions. If you receive an email that appears to be from someone legitimate, but you are still unsure; pick up the phone and verify they sent that email.
Email Sample from an attack:
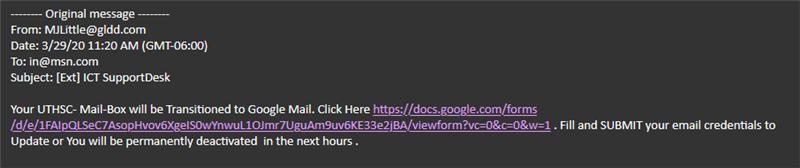
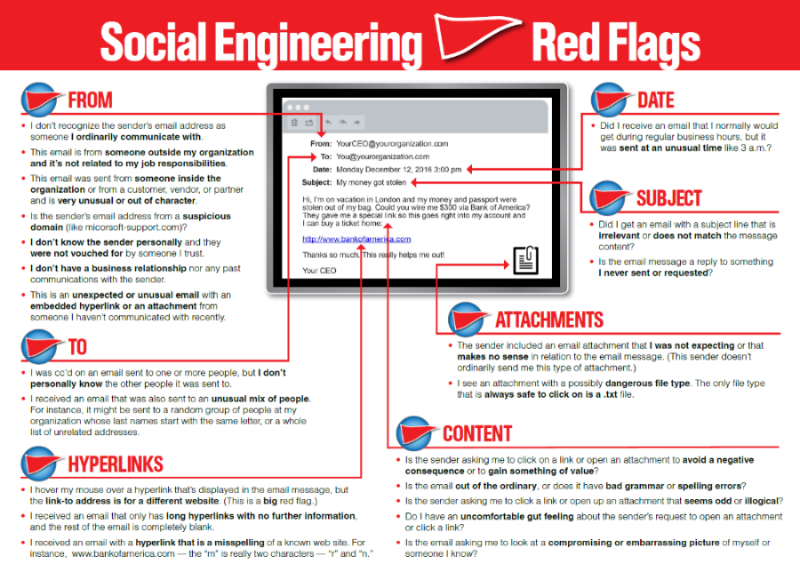
Triage of above email with Red Flags that this is nefarious:
- The From line is not @UTHSC.edu – our help desk and official emails come from UTHSC.edu
- The to: address is not yours; this is a group created from collected emails through other social engineering attacks
- Subject line states ICT Support Desk; ours is currently ITS Help Desk
- Directions state your mailbox is moving to google Mail; this would not occur without a heavily communicated campaign and through official UTHSC channels
- The link is to a Google document; this is rapidly becoming an attack platform which makes circumventing spam filters easy.
- The instructions request you enter your username (we refer to them as NETIDs at UTHSC) and password; we will never request that. This is the standard credential harvesting attack; it hopes to collect credentials with privileged rights.
- The instructions present a sense of urgency; (permanently deactivated in the next hours) again we would not create such a restrictive requirement on a major IT change like this.
22 Red Flags in Emails